, , , , , , , , , , , , , , , , , , , , , , , , , , , ,
Restrict articles to display by their associated tags. Articles can have multiple tags and can be further restricted with the "and" or search relation.
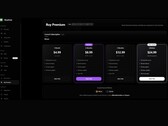
, , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , , ,
Search by article title: