The world of cyber security is fast paced and always changing. Security specialists have to stay on top of their game as hackers and criminals use increasingly creative methods to break into systems. One of the latest threats comes through an unexpected avenue: subtitles.
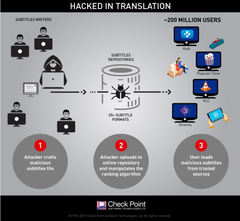
Media programs like VLC, Kodi (formerly XBMC), and strem.io commonly have repositories of subtitles for movies, TV shows, and other media. Users can download subtitles from these repositories and load them into their media application of choice. However, some clever hackers have been injecting malicious code into subtitle files in these repositories. One the subtitle file is loaded by the user, the code activates and allows the perpetrator to seize control of whatever device loaded the subtitle.
After loading the malicious file into a subtitles repository, the hackers were able to manipulate the ranking system to make their file appear at the top of a search list, greatly increasing the likelihood of their file being downloaded. According to cyber security research firm Check Point, who discovered the vulnerability, this attack is “one of the most widespread, easily accessed and zero-resistance vulnerability (sic) reported in recent years.”
This attack is indeed incredibly surreptitious. Since the malicious code is loaded through simple, unassuming text files used for movie subtitles, security firms never thought to examine them. Antivirus was never tuned to check through subtitle files. And the fact that the malicious files came from repositories of some of the largest media applications in the world, they were assumed to be trusted and vetted files.
Check Point estimates that the total number of vulnerable users is in the “hundreds of millions.” VLC alone has been downloaded over 2 billion times, and the most recent version at the time the attack was discovered (2.2.4) had eclipsed 170 million downloads. Kodi, which was formerly known as XBox Media Center, or XBMC, routinely hits “40 million unique users each month,” according to Check Point.
As of this writing, Check Point has “found vulnerabilities in four of the most prominent media players.” These include VLC, Kodi, Popcorn Time, and Stremio. Check Point also stated that they “[have] reason to believe similar vulnerabilities exist in other media players as well.” The security firm is working with the developers of these software packages to patch the vulnerability.
Currently, Popcorn Time, Kodi, VLC, and Stremio have created fixed versions, all of which are available for download at the following sites:
- Popcorn Time - https://ci.popcorntime.sh/job/Popcorn-Time-Desktop/249
- Kodi - https://kodi.tv/download
- VLC - http://get.videolan.org/vlc/2.2.5.1/win32/vlc-2.2.5.1-win32.exe
- Stremio - https://www.strem.io/
Users of other media streaming software should check with the application developers to see if a fix is available.
For more information on this attack, visit Check Point’s blog here. You can also see a demonstration of the exploit at work in the video below.