If WannaCry and the recent media player attacks haven’t yet made you concerned about cyber security, a long-conjectured exploit in Android has now been confirmed by researchers at the Georgia Institute of Technology and the University of California.
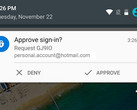
Dubbed “Cloak and Dagger” or “Tapjacking,” the exploit uses two permissions to gain full access to a targeted device. Here’s the pinch: the permissions are often granted without the user’s knowledge. The permissions needed for the exploit to work are the SYSTEM_ALERT_WINDOW and BIND_ACCESSIBILITY_SERVICE, or the “draw on top” and “a11y,” permissions. SYSTEM_ALERT_WINDOW is used by apps to draw overlays on top of the screen, á la Facebook Messenger’s chat heads. This permission is automatically granted to apps that request it if installed via the Google Play Store. Using this permission, the malicious app can draw invisible overlays on the screen without the user knowing they’re there. The overlays can then relay data, such as tapped areas on the screen, and be used to parse user input into the app. Using this permission alone, a nefarious party can use an invisible overlay drawn over the keyboard area to ascertain user passwords and sensitive messages. Worse yet, these invisible overlays can be used to trick the users into granting the a11y permission.
BIND_ACCESSIBILITY_SERVICE (a11y) can be a dangerous permission to grant, as it can allow an app deep control over the entire system. It’s often used for legitimate purposes, such as in battery saver apps or other monitoring/control apps. However, researchers showed that by granting the a11y permission, an app can then trigger every other permission possible, enabling a “God Mode” that allows the app to do anything on the infected phone. This can include activating the camera, connection to specific networks, or even sending user data, all without the knowledge of the user. In the video below, the researchers show off one of these “God Mode” apps and how powerful (and malicious) they can be.
So what about a fix? Surprisingly, Google hasn’t stated that they’ll be patching the problem anytime soon. With the exploit afflicting Android versions 5.1.1 through the latest 7.1.2, this leaves a huge array of devices vulnerable. Android O might mitigate the issue as it will notify users when an app is using an overlay. However, this “solution” is highly dependant on the end user being attentive and understanding the risk this can pose. A representative for Google also said that Play Store Protect will “detect and prevent the installation of [the malicious] apps.”
As with all types of malware, the best defense is information. Users should remain attentive and be highly critical of apps that request permissions, especially those that request a11y Accessibility permissions. Stay vigilant, Android users!