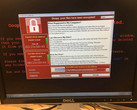
If you were unfortunate enough to be one of those users who affected by the recently-patched Microsoft Office bug, Microsoft’s recent patch may not be enough to put you at ease as it appears that more attackers were using the exploit than previously thought. The vulnerability was originally thought to be limited to just three known attackers, but research groups have discovered that more organizations were using the exploit as early as January.
The exploit takes the form of a file masquerading as a harmless Word document; in reality, the Rich Text file downloads a malicious HTML application from a server. The application then downloads and runs a script that can be used to install malware without the user’s knowledge.
Among the groups is FinSpy, which used the bug to install a spy program for carrying out espionage. The group has ties to state-sponsored groups. FinSpy is associated with Germany and UK-based “lawful intercept” from Gamma Group.
FireEye was unwilling to discuss who was behind the attacks. According to the report, only one FinSpy user has been observed leveraging this zero-day exploit. “The historic scope of FinSpy, a capability used by several nation-states, suggests other customers had access to it,” the report says.
Microsoft patched the exploit on Tuesday, but not all machines have updated to the latest patch and as a result remain vulnerable.