The white-hat firm Checkmarx has recently gone public about a severe potential exploit it allegedly found in the Google and Samsung Camera apps, which are installed on hundreds of millions of phones out there. This issue was apparently related to the common vulnerability known as CVE-2019-2234. It is described as a direct pathway to control of the apps in question in a way that could have allowed a bad actor to open and operate image sensors without the owner's knowledge.
Remote access such as this is normally protected against by a system of user-input-dependent permission controls called for in the Android operating system. However, Checkmarx asserts that CVE-2019-2234 resulted in the ability to bypass these restrictions entirely. The group developed their own app that required nothing more than the 'storage' permission in order to gain control of the camera as they described in order to prove this.
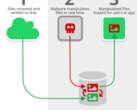
Once this app was on a device, Checkmarx reportedly demonstrated that it was possible for it to set up a connection to a command and control server that persisted even if said app was closed thereafter. This app was then allegedly capable of initializing cameras on the phone in question, then taking photos or videos at will and sending them back to this server. In addition, files already in the device's memory were also liable to be sent to this server.
Furthermore, the group claimed that their app was also capable of controlling device GPS in order to steal a user's location without their knowledge. However, fortunately, this potential doorway to hacking has been closed. Checkmarx reported its findings to Google and Samsung in July 2019, which led to software updates intended to address the CVE in question.
Therefore, its worrying implications should not apply to devices with relatively recent upgrades or security patches. Nevertheless, it may be a valuable cautionary tale with the moral that it is always wise to keep an eye on your device's hardware and what might have access to it.