If you are currently using a Dell laptop or desktop that features Dell SupportAssist, you might want to quickly check which version you are using. A vulnerability has been discovered in the utility that affects Dell SupportAssist for Business PCs version 2.0 and Dell SupportAssist for Home PCs version 3.2.1 or earlier.
The vulnerability was unearthed by cybersecurity researchers at SafeBreach, who realized that weaknesses in the application’s structure could allow hackers to penetrate the system affected and even take control over the computer, or as SafeBreach’s press release disturbingly worded it:
[…] giving them near total control over what’s happening on that machine and the ability to read, copy or alter any data in physical memory.
Fortunately, the cybersecurity company has contacted both Dell and PC-Doctor, which is the company that created SupportAssist, to inform them of its findings. It’s not just Dell that is the only OEM affected though; any computer running this particular software from PC-Doctor will require a patch to prevent a hacker taking advantage of the vulnerability.
Dell has published a security advisory, which can be accessed here. It offers a straightforward resolution for the potential threat, which involves updating the relevant software that now includes a fix provided by PC-Doctor.
Source(s)
SUNNYVALE, Calif., June 21, 2019 (GLOBE NEWSWIRE) -- SafeBreach, a leader in breach and attack simulation, today announced that it has discovered a major security vulnerability potentially affecting several million laptops and desktops made by Dell Computer and several other Original Equipment Manufacturers (OEMs). The vulnerability exploits a security hold in software manufactured by PC-Doctor that is used as part of Dell SupportAssist software. SupportAssist performs health checks on system hardware and software, verifying that a machine is working as intended.
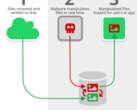
The vulnerability exploits weaknesses in the library structure of the application including the lack of digital certificate validation in a key process that allows for access to physical memory. In a Proof-of-Concept, the SafeBreach research team demonstrated that attacking this vulnerability would allow attackers to access and read or write to the physical memory of systems. This would enable them to install malicious executables or otherwise compromise the system and achieve admin-level permissions on the system, giving them effective control.
“This is a serious security issue that would allow attackers access to system-level capabilities, giving them near total control over what’s happening on that machine and the ability to read, copy or alter any data in physical memory,” said Itzik Kotler, CTO and Co-Founder of SafeBreach. “We urge everyone who has purchased a machine that uses PC-Doctor software as part of its health check system to upgrade and patch their machines as quickly as possible.”
SafeBreach reported the vulnerability (CVE-2019-12280) to Dell and PC-Doctor upon discovery in late May.
Dell response: “PC-Doctor released the fix to Dell. Dell implemented the fix and released updates on May 28, 2019 for the affected Dell SupportAssist for Business PCs and Dell SupportAssist for Home PCs versions. More than 90% of customers to date have received the update and are no longer as risk. Most customers have automatic updates enabled, which is a general security best practice to keep software and systems up to date. Dell urges customers to turn on automatic updates or manually update their SupportAssist software. Dell’s first priority is product security and helping our customers ensure the security of their data and systems. Customers can find more information within the Dell security advisory DSA-2019-084.”
The vulnerability was the latest discovered by SafeBreach Labs as part of the company’s efforts to make all computing systems more secure and reliable. For more details on this research go to: safebreach.com/Post/<wbr />OEM-Software-Puts-Multiple-<wbr />Laptops-At-Risk