Earlier this week, it emerged that a vulnerability in Cyberpunk 2077 left PCs open to malicious code, a problem that CDPR was reputedly warned about before issuing Hotfix 1.11 last month. The vulnerability only applied to games that had been modded or that used custom saves, but it was serious enough for CDPR to issue a statement on the matter, warning people against customising the game in any way.
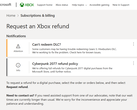
Thankfully, the company has now published Hotfix 1.12, which addresses the problem. The changelog is as follows:
This update addresses the vulnerability that could be used as part of remote code execution (including save files):
Fixed a buffer overrun issue.
Removed/replaced non-ASLR DLLs.
The vulnerability only affected Cyberpunk 2077 on PC, so PlayStation, Xbox and Stadia owners will not receive Hotfix 1.12. Response from fans has been good, overall, at least on CDPR's forums. Unsurprisingly, Hotfix 1.12 is only a few megabytes and should install almost instantly if it has not already done so. The hotfix's size suggests that CDPR has not changed anything outside of addressing the vulnerability, but any other issues should probably emerge within the next few days.
CDPR is due to release another patch for Cyberpunk 2077 too. Seemingly called Patch 1.2, CDPR has previously stated that it would be a more significant update to the game than Patch 1.1, which the company delivered last month. There is no word on additional patches beyond Patch 1.2 for the time being, though.