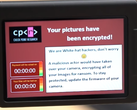
Security research firm Dataviper unveiled what could be the world's largest data breach till date. 1.2 billion users' personal information such as names, email addresses, phone numbers, and employment details have been leaked online. The leak originated from two Data Enrichment firms: People Data Labs and Oxydata.
Data Enrichment firms aggregate user information obtained from multiple sources. For example, a firm can use a person's name and telephone number to fish out their employment details, spending patterns, and even political leanings. Platforms such as Facebook, Instagram, and Linkedin are often the source of such data.
The report further adds that anyone could access the server by navigating to 35.199.58.125 (URL is defunct now, for obvious reasons.) The server hosted 4 TB of data that consisted of 4 billion user profiles. Why was such a massive cache of highly sensitive information stored with virtually no security on a publicly accessible server? Nobody seems to know the answer to that yet.
Dataviper reached out to People Data Labs and Oxydata for comment and is yet to receive one from either firm. Furthermore, the server's cloud provider also refused to comment on the matter, citing user privacy. It's hard to determine who is responsible for the leak at this point, as both companies have denied ownership of the server. Dataviper's research indicates that the statement is true, and the server was indeed run by a third party.
The likelihood of the culprit being an errant employee from either firm is low, considering that two separate companies' data was hosted on one server. Prima facie, it seems as if someone managed to get their hands on both data caches and decided that it would be best to dump them on one server.
To check if you've been affected by the leak, simply go here and input your email ID. The page will tell you if you've been affected by this breach. If you find your name on the list, we recommend that you change all your passwords and enable two-factor authentication wherever possible.