Just ahead of Microsoft’s Surface Book 3 launch, a leaked video presentation for the Surface 3 laptop shows a company exec reveal that its reason for avoiding Thunderbolt 3 has been because of security concerns. Specifically, Thunderbolt 3 grants direct access to system memory and this is something Microsoft has wanted to avoid. Naturally, this raised alarm bells for the impending launch of the Surface Book 3 which was then on the immediate horizon.
Sure enough, when the Surface Book 3 was unveiled it last week, it once again omitted a Thunderbolt 3 port to the dismay of many Windows fans. After all, Thunderbolt 3 offers a theoretical maximum throughput of 40 Gbps which offers the ability to access the fastest external storage drives and external GPU enclosures among other benefits. It is also a standard feature on many similar high-end notebooks, so what gives?
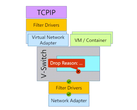
Now a new piece of research from security specialist Björn Ruytenberg has revealed that any Windows or Linux PC made before 2019 is vulnerable to the “evil maid” hack that he is calling “Thunderspy”. It requires gear worth around US$400 but it can bypass the login screen of a sleeping or locked computer and access all the data on its drive -- even if it is encrypted. The exploit won’t work in macOS but will on a Mac running Windows in Boot Camp.
The solution:
If you intend to use Thunderbolt connectivity, we strongly recommend to: Connect only your own Thunderbolt peripherals; never lend them to anybody; avoid leaving your system unattended while powered on, even when screenlocked; avoid leaving your Thunderbolt peripherals unattended; ensure appropriate physical security when storing your system and any Thunderbolt devices, including Thunderbolt-powered displays; consider using hibernation (Suspend-to-Disk) or powering off the system completely. Specifically, avoid using sleep mode (Suspend-to-RAM).
Wired, in breaking the story, noted that Intel’s new Kernel DMA Protection feature [built following advice of the hack three months ago] needs to be enabled to protect against the attack. However, the response from OEMs varied as to whether is enabled by default on their machines. Even then, Ruytenberg advised that Intel will need to make yet another silicon level fix to completely eliminate the attack. Intel’s response to Wired reads: "For all systems, we recommend following standard security practices, including the use of only trusted peripherals and preventing unauthorized physical access to computers."