We’ve reported on the various security holes in smartphones in the past. All of these vulnerabilities have been found in software, which can be quickly patched via over-the-air updates. However, a new research paper by a group at the University of the Negev details a previously unknown flaw in smartphone security: physical hardware.
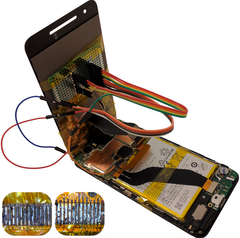
The paper’s authors demonstrated how they were able to take full control of a Nexus 6P by using a third-party replacement touchscreen. The team injected malicious code into the Synaptics S3718 drivers used by the device. According to the paper, a “component driver’s source code implicitly assumes that the component hardware is authentic and trustworthy.” After figuring out how the touchscreen accessed the kernel of the driver and interacted with the device itself, the authors were able to execute arbitrary code and seize control of the phone. In short, the arbitrary code execution allowed the team to allow any application to gain root access, disable or bypass any preventative measure designed to halt malicious code execution at the kernel level, and create new backdoors within the kernel. The device in question was a freshly reset Nexus 6P with a locked bootloader, which makes the exploit even more impressive and worrisome.
In a demonstration video, the team used the injected malicious code to automatically install malware and grant it root access, access and use the camera, alter URLs to redirect users to phishing sites, and log the phone’s unlock pattern. The team has also successfully executed this attack on a Galaxy S5, Nexus 5X, and Nexus 5, all of which use Synaptics touchscreen drivers.
So what can you do to avoid these kinds of attacks? The best prevention is to only use OEM parts for smartphone repairs. If you don’t feel comfortable repairing the phone yourself, send it to the phone maker or a certified repair technician that will use OEM replacement parts. Don’t purchase replacement parts from sketchy or unknown sources. The paper’s authors also suggest that smartphone manufacturers start including hardware-based firewalls to protect the device from similar attacks.
The full paper can be found here.